A network is simply a way for machines/computers to communicate. 
At the physical level, it consists of all the machines you want to connect and the devices you use to connect them. Individual machines are connected either with a physical connection (a category 5 cable going into a network interface card, or NIC) or wirelessly. To connect multiple machines, each machine must connect to a hub or switch, and then those hubs/switches must connect. In larger networks, each subnetwork is connected to the others by a router.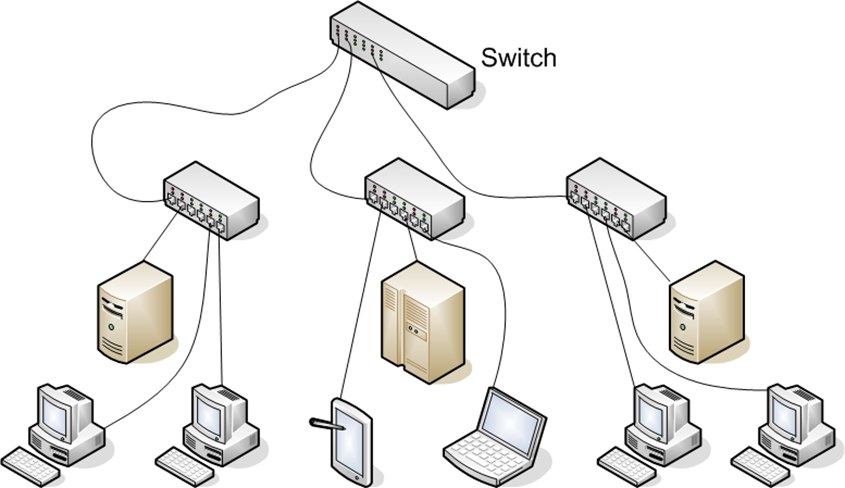
1.1.1 Basic Network Structure
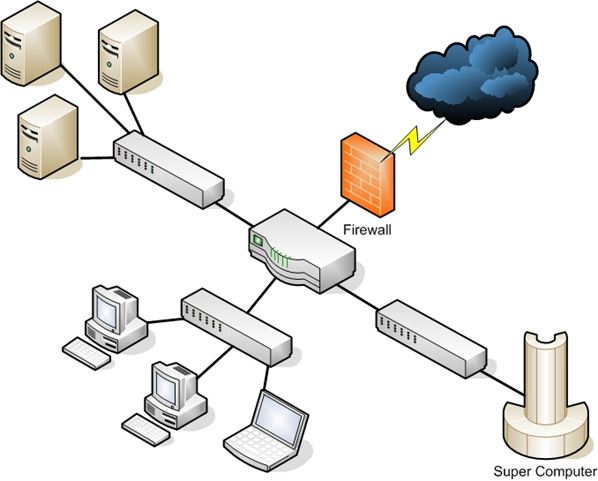
Some connection point(s) must exist between your network and the outside world. A barrier is set up between that network and the Internet, usually in the form of a firewall. The real essence of networks is communication allowing one machine to communicate with another.
However, every path of communication is also a possibility of an attack.
The first step in understanding how to defend a network is having a detailed understanding of how computers communicate over a network. Network interface cards, switches, routers, hubs, and firewalls are the fundamental physical pieces of a network. The way they are connected and the format they use for communication is the network architecture.
1.1.2 Data Packets
After you have established a connection with the network (whether it is physical or wireless), you need to send data. The first part is to identify where you want to send it. All computers (as well as routers and switches) have an IP address that is a series of four numbers between 0 and 255 and is separated by periods, such as 192.168.0.1.
The second part is to format the data for transmission. All data is in binary form (1s and 0s). This binary data is put into packets, all less than about 65,000 bytes. The first few bytes are the header. That header tells where the packet is going, where it came from, and how many more packets are coming as part of this transmission. There is more than one header, but for now, we will just discuss the header as a single entity. Some attacks (IP spoofing, for example) try to change the header of packets to give false information. Other methods of attacks simply try to intercept packets and read the content (thus compromising the data).
A packet can have multiple headers. Most packets will have at least three headers. The IP header has information such as IP addresses for the source and destination, as well as what protocol the packet is. The TCP header has information such as a port number. The Ethernet header has information such as the MAC address for the source and destination. If a packet is encrypted with Transport Layer Security (TLS), it will also have a TLS header.
1.1.3 IP Addresses
The first major issue to understand is how to get packets to their proper destination. Even small networks have many computers that could potentially be the final destination of any packet sent. The Internet has millions of computers spread out across the globe. How do you ensure that a packet gets to its proper destination? The problem is not unlike addressing a letter and ensuring it gets to the correct destination. Let’s begin by looking at IP version 4 addressing because it is the most common in use today. This section also briefly discusses IP version 6.
An IP version 4 address is a series of four three-digit numbers separated by periods (An example is 192.168.1.1.) Each of the three-digit numbers must be between 0 and 255. An address of 192.168.0.257 would not be a valid one. The reason for this rule is that these addresses are four binary numbers: The computer simply displays them to you in decimal format.
Table 1–1 IP version 4 Address
Recall that 1 byte is 8 bits (1s and 0s), and an 8-bit binary number converted to decimal format will be between 0 and 255. The total of 32 bits means that approximately 4.2 billion possible IP version 4 addresses exist.
Table 1–2 Decimal-to-Binary Conversion Example
The IP address of a computer tells you a lot about that computer. The first byte (or the first decimal number) in an address reveals what network class that machine belongs to. Table 1–3 summarizes the five network classes.
Table 1–3 Five Network Classes
The IP range of 127 is not listed in the above table. The IP address 127.0.0.1 designates the machine you are on, regardless of the IP address assigned to your machine. This address is referred to as the loopback address. That address is used in testing the machine and the NIC card.
These particular classes are important as they tell you what part of the address represents the network and what part represents the node. For example, in a Class A address, the first octet represents the network, and the remaining three represent the node. In a Class B address, the first two octets represent the network, and the second two represent the node. And finally, in a Class C address, the first three octets represent the network, and the last represents the node. There are also some very specific IP addresses and IP address ranges you should be aware of.
The first, as previously mentioned, is 127.0.0.1, or the loopback address. It is another way of referring to the network interface card of the machine you are on. Private IP addresses are another issue to be aware of. Certain ranges of IP addresses have been designated for use within networks.
These cannot be used as public IP addresses but can be used for internal
Workstations and servers. Those IP addresses are:
Sometimes people who are new to networking, have some trouble understanding public and private IP addresses. A good example is an office building. Within a single office building, each office number must be unique. You can only have one 101. And within that building, if you refer office 101 it is immediately clear what you are talking about.
But there are other office buildings, many of which have their own office 101. You can think of private IP addresses as office numbers. They must be unique within their network, but there may be other networks with the same private IP. Public IP addresses are more like traditional mailing addresses. Those must be unique worldwide.
When communicating from office to office you can use the office number, but to get a letter to another building you have to use the complete mailing address. It is much the same with networking. You can communicate within your network using private IP addresses, but to communicate with any computer outside your network, you have to use public IP addresses.
One of the roles of a gateway router is to perform what is called network address translation (NAT). Using NAT, a router takes the private IP address on outgoing packets and replaces it with the public IP address of the gateway router so that the packet can be routed through the Internet.
We have already discussed IP version 4 network addresses. Now let’s turn our attention to subnetting. Subnetting is simply splitting up a network into smaller portions. For example, if you have a network using the IP address 192.168.1.X (X being whatever the address is for the specific computer), then you have allocated 255 possible IP addresses. What if you want to divide that into two separate subnetworks? Subnetting is how you do that.
More technically, the subnet mask is a 32-bit number that is assigned to each host to divide the 32-bit binary IP address into network and node portions. You also cannot just put in any number you want. The first value of a subnet mask must be 255; the remaining three values can be 255, 254, 252, 248, 240, 224, or 128. Your computer will take your network IP address and the subnet mask and use a binary AND operation to combine them.
It may surprise you to know that you already have a subnet mask even if you have not used subnetting. If you have a Class C IP address, then your network subnet mask is 255.255.255.0. If you have a Class B IP address, then your subnet mask is 255.255.0.0. And finally, if it is Class A, your subnet mask is 255.0.0.0.
Now think about these numbers in relationship to binary numbers. The decimal value 255 converts to 11111111 in binary. So you are literally “masking” the portion of the network address that is used to define the network, and the remaining portion is used to define individual nodes. Now if you want fewer than 255 nodes in your subnet, then you need something like 255.255.255.240 for your subnet. If you convert 240 to binary, it is 11110000. That means the first three octets and the first 4 bits of the last octet define the network. The last 4 bits of the last octet defines the node. That means you could have as many as 1111 (in binary) or 15 (in decimal) nodes on this subnetwork. This is the basic essence of subnetting.
Subnetting only allows you to use certain, limited subnets. Another approach is CIDR or classless interdomain routing. Rather than define a subnet mask, you have the IP address followed by a slash and a number. That number can be any number between 0 and 32, which results in IP addresses like these:
- 192.168.1.10/24 (basically a Class C IP address)
- 192.168.1.10/31 (much like a Class C IP address with a subnet mask)
When you use this, rather than having classes with subnets, you have variable-length subnet masking (VLSM) that provides classless IP addresses. This is the most common way to define network IP addresses today.
You should not be concerned that new IP addresses are likely to run out soon. The IP version 6 standard is already available and methods are in place already to extend the use of IPv4 addresses. The IP addresses come in two groups: public and private.
The public IP addresses are for computers connected to the Internet. No two public IP addresses can be the same. However, a private IP address, such as one on a private company network, has to be unique only in that network. It does not matter if other computers in the world have the same IP address, because this computer is never connected to those other worldwide computers.
Network administrators often use private IP addresses that begin with a 10, such as 10.102.230.17. The other private IP addresses are 172.16.0.0–172.31.255.255 and 192.168.0.0–192.168.255.255.
Also, note that an ISP often will buy a pool of public IP addresses and assign them to you when you log on. Therefore, an ISP might own 1,000 public IP addresses and have 10,000 customers. Because all 10,000 customers will not be online at the same time, the ISP simply assigns an IP address to a customer when he or she logs on, and the ISP un-assigns the IP address when the customer logs off.
IPv6 utilizes a 128-bit address (instead of 32) and utilizes a hex numbering method to avoid long addresses such as 132.64.34.26.64.156.143.57.1.3.7.44.122.111.201.5.
The hex address format appears in the form of 3FFE:B00:800:2::C, for example. This gives you 2128 possible addresses (many trillions of addresses), so no chance exists of running out of IP addresses soon.
There is no subnetting in IPv6. Instead, it only uses CIDR. The network portion is indicated by a slash followed by the number of bits in the address that are assigned to the network portion, such as
There is a loopback address for IPv6, and it can be written as::/128.
Other differences between IPv4 and IPv6 are described here:
1.1.4 Uniform Resource Locator (URL)
- Link/machine-local.
- IPv6 version of IPv4’s APIPA or Automatic Private IP Addressing. So if the machine is configured for dynamically assigned addresses and cannot communicate with a DHCP server, it assigns itself a generic IP address. DHCP, or Dynamic Host Configuration Protocol, is used to dynamically assign IP addresses within a network.
- IPv6 link/machine-local IP addresses all start with fe80::. So if your computer has this address, that means it could not get to a DHCP server and therefore made up its generic IP address.
- Site/network-local.
- IPv6 version of IPv4 private address. In other words, these are real IP addresses, but they only work on this local network. They are not routable on the Internet.
- All site/network-local IP addresses begin with FE and have C to F for the third hexadecimal digit: FEC, FED, FEE, or FEF.
- DHCPv6 uses the Managed Address Configuration Flag (M flag).
- When set to 1, the device should use DHCPv6 to obtain a stateful IPv6 address.
- Other stateful configuration flags (O flag).
- When set to 1, the device should use DHCPv6 to obtain other TCP/IP configuration settings. In other words, it should use the DHCP server to set things like the IP address of the gateway and DNS servers.
For most people, the main purpose of getting on the Internet is web pages (but there are other things such as e-mail and file downloading). If you had to remember IP addresses and type those in, then surfing the Net would be difficult. Fortunately, you do not have to. You type in domain names that make sense to humans and those are translated into IP addresses. For example, you might type in www.microsoft.com to go to Microsoft’s website.
Your computer, or your ISP, must translate the name you typed in (called a Uniform Resource Locator, or URL) into an IP address. The DNS (Domain Name Service) protocol, which is introduced along with other protocols a bit later, handles this translation process. Therefore, you are typing in a name that makes sense to humans, but your computer is using a corresponding IP address to connect. If that address is found, your browser sends a packet (using the HTTP protocol) to TCP port 80. If that target computer has software that listens and responds to such requests (like web-server software such as Apache or Microsoft Internet Information Services), then the target computer will respond to your browser’s request and communication will be established.
This method is how web pages are viewed. If you have ever received an Error 404: File Not Found, what you’re seeing is that your browser received back a packet (from the webserver) with error code 404, designating that the web page you requested could not be found. The web server can send back a series of error messages to your web browser, indicating different situations.
E-mail works the same way as visiting websites. Your e-mail client will seek out the address of your e-mail server. Then your e-mail client will use either POP3 to retrieve your incoming e-mail, or SMTP to send your outgoing e-mail. Your e-mail server (probably at your ISP or your company) will then try to resolve the address you are sending to. If you send something to [email protected], your e-mail server will translate that e-mail address into an IP address for the e-mail server at gmail.com, and then your server will send your e-mail there. Note that newer e-mail protocols are out there; however, POP3 is still the most commonly used.
1.1.5 MAC Addresses
IMAP is now widely used as well. Internet Message Access Protocol operates on port 143. The main advantage of IMAP over POP3 is it allows the client to download only the email headers, and then the user can choose which messages to fully download. This is particularly useful for smartphones.
MAC addresses are an interesting topic. A MAC address is a unique address for a network interface card (NIC). Every NIC in the world has a unique address that is represented by a six-byte hexadecimal number. The Address Resolution Protocol (ARP) is used to convert IP addresses to MAC addresses. So, when you type in a web address, the DNS protocol is used to translate that into an IP address. The ARP protocol then translates that IP address into a specific MAC address of an individual NIC.
1.1.6 Protocols
IEEE assigns the first three bytes (24 bits) of the MAC address to a vendor. This part of the address is known as the Organizationally Unique Identifier (OUI). The OUI helps professionals to determine the MAC address manufacturer. The remaining three bytes (24 bits) are assigned by the vendor. The MAC address is equal to 48 bits.
Different types of communications exist for different purposes. The different types of network communications are called protocols. A protocol is, essentially, an agreed method of communication. This definition is exactly how the word protocol is used in standard, non-computer usage. Each protocol has a specific purpose and normally operates on a certain port. The table below lists some of the most important protocols.
You should note that this list is not complete and hundreds of other protocols exist. All these protocols are part of a suite of protocols referred to as TCP/IP (Transmission Control Protocol/Internet Protocol).
The most important thing for you to realize is that the communication on networks takes place via packets, and those packets are transmitted according to certain protocols, depending on the type of communication that is occurring.
You might be wondering what a port is. Don’t confuse this type of port with the connections on the back of your computers, such as a serial port or parallel port. A port in networking terms is a handle, a connection point. It is a numeric designation for a particular pathway of communications.
All network communication, regardless of the port used, comes into your computer through the connection on your NIC. You might think of a port as a channel on your TV. You probably have one cable coming into your TV but you can view many channels. You have one cable coming into your computer, but you can communicate on many different ports
STAY TUNED FOR THE MORE INTERESTING ARTICLES RELATED TO NETWORKING.....................TILL THEN KEEP LEARNING AND COMMENT DOWN AND TELL WHICH TOPIC YOU WANT NEXT :)
Comments
Post a Comment